Configuring Synology NAS for Secure Remote Access
Introduction
In order to ensure secure remote access to your Synology NAS, it is important to follow specific steps and configurations. This guide provides a detailed walkthrough to help you set up your NAS for secure remote access.
Step 1: Enabling DSM Firewall
In your Synology NAS Control Panel, navigate to "Security" and enable the built-in DSM Firewall. This firewall provides network-level protection and helps safeguard your NAS from unauthorized access.
Step 1.1: Firewall Rules Configuration
Within the DSM Firewall settings, create specific firewall rules to allow inbound traffic for the desired remote access services, such as SSH, VPN, or FTP. Limit access to known IP addresses and networks to enhance security.
Step 2: Configuring Port Forwarding
Port forwarding allows external requests to reach your Synology NAS through your router. Open your router's administration panel and configure port forwarding to forward the necessary ports to your NAS's local IP address.
Step 2.1: Choosing and Forwarding Specific Ports
Identify the ports required for the remote access services you want to use (e.g., 5001 for HTTPS, 22 for SSH) and configure the port forwarding settings accordingly. Be sure to forward only the necessary ports to minimize potential vulnerabilities.
Step 3: Setting Up a Secure Connection
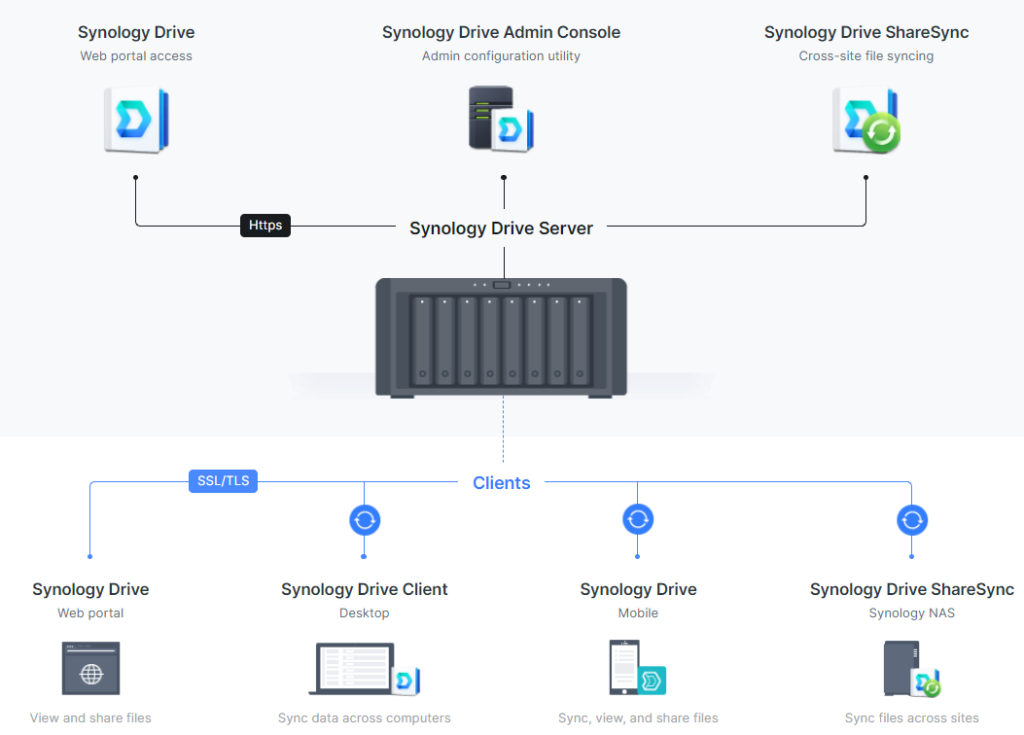
To ensure secure remote access, it is recommended to use a secure connection method such as VPN or SSL/TLS encryption. This step-by-step guide focuses on SSL/TLS.
Step 3.1: Obtaining a SSL/TLS Certificate
Acquire an SSL/TLS certificate for your NAS's domain or subdomain to enable secure connections. You can either obtain a certificate from a trusted Certificate Authority or set up a self-signed certificate. Remember to set a strong password for the private key associated with the certificate.
Step 3.2: Enabling HTTPS on Your NAS
In the Control Panel of your Synology NAS, go to "Network" and enable the HTTPS service. Choose the SSL/TLS certificate you obtained in the previous step and configure the necessary HTTPS settings. This ensures encrypted communication between your NAS and remote devices.
Step 4: Configuring User Access Controls
To enhance security, carefully manage user access controls and permissions on your Synology NAS.
Step 4.1: Creating Secure User Accounts
Create individual user accounts for remote access, enabling strong passwords and two-factor authentication for additional security. Assign appropriate access permissions to these accounts, allowing them to access the necessary files and services without compromising the overall system's integrity.
Step 4.2: Implementing Account Lockout Policies
Increase security by implementing account lockout policies that automatically lock user accounts after a certain number of failed login attempts. This helps mitigate the risk of brute-force attacks on your NAS.
Step 5: Regularly Updating DSM and Installed Packages
Keep your DSM (DiskStation Manager) and installed packages up to date. Regular software updates include security patches that address vulnerabilities and enhance system protection.
Conclusion
Following this comprehensive guide will ensure that your Synology NAS is properly configured for secure remote access. By enabling necessary security measures, such as firewall rules, port forwarding, SSL/TLS encryption, and user access controls, you can minimize potential risks and protect your data and network.